OpenAI’s GPT-5.5-Cyber Is Really About Permissioning Cyber Capability
OpenAI’s announcement of GPT-5.5 with Trusted Access for Cyber and the limited preview of GPT-5.5-Cyber is not just another model release. The more important shift is access control.
The core problem is simple: the same cybersecurity request can be either defensive or harmful depending on who is asking, what system they are targeting, and whether the work is authorized. A proof-of-concept for a public CVE can help a defender validate a patch in a controlled environment. The same kind of request against a third-party target can become an attack workflow.
Generic refusals are too blunt for this problem. They reduce risk, but they also slow down legitimate defenders.
Trusted Access for Cyber is OpenAI’s answer: an identity and trust-based framework that gives verified defenders lower refusal friction for authorized security workflows while continuing to block harmful activity such as credential theft, persistence, malware deployment, or exploitation of third-party systems.
OpenAI separates the current access model into two main layers.
GPT-5.5 with Trusted Access for Cyber is the recommended starting point for most defenders. It supports workflows such as secure code review, vulnerability triage, malware analysis, detection engineering, and patch validation while preserving the broader safety posture of GPT-5.5.
GPT-5.5-Cyber is narrower. It is in limited preview for more specialized dual-use workflows, including authorized red teaming and penetration testing where defenders may need to validate exploitability in a controlled environment.
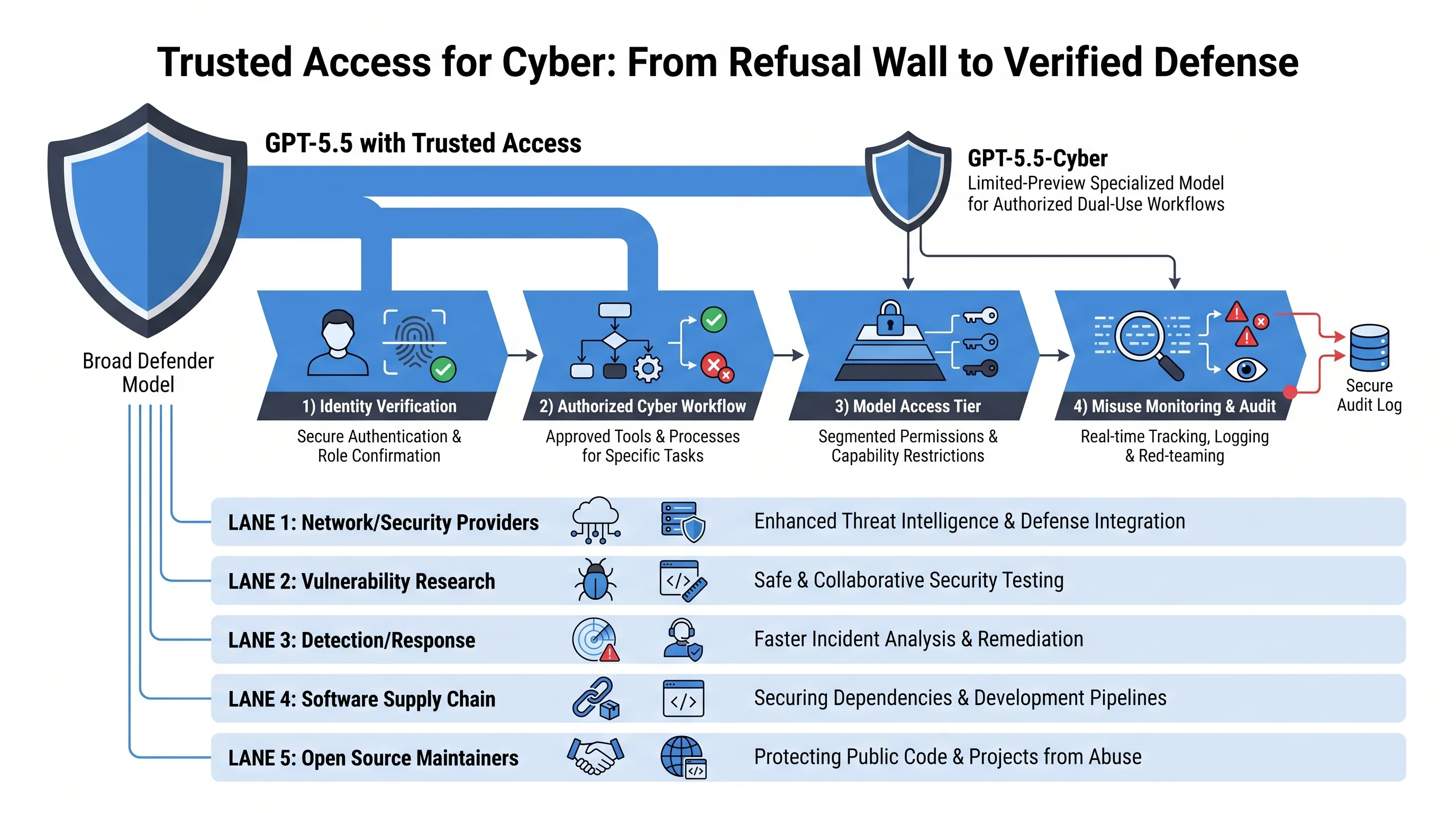
OpenAI is explicit that this first preview of GPT-5.5-Cyber is not meant to significantly outperform GPT-5.5 across every cyber evaluation. It is primarily trained to be more permissive for security-related tasks under stronger verification, monitoring, approved-use scoping, and partner feedback.
That detail matters. The release is less about raw offensive capability and more about controlled permissioning.
The ecosystem strategy is also notable. OpenAI describes a defensive flywheel across network and security providers, vulnerability research, detection and response, software supply chain security, and open source maintenance.
Partners named in the post include Cisco, CrowdStrike, Palo Alto Networks, Zscaler, Cloudflare, Akamai, Fortinet, Intel, Qualys, Rapid7, Tenable, Trail of Bits, SpecterOps, Snyk, Gen Digital, Semgrep, and Socket.
The goal is to move faster across the full security lifecycle: finding vulnerabilities, validating criticality, reviewing patches, drafting detections, connecting telemetry, deploying WAF mitigations, and preventing risky dependencies from reaching production.
OpenAI also ties this to Codex Security, which helps teams build codebase-specific threat models, explore realistic attack paths, validate issues in isolated environments, and propose patches for human review.
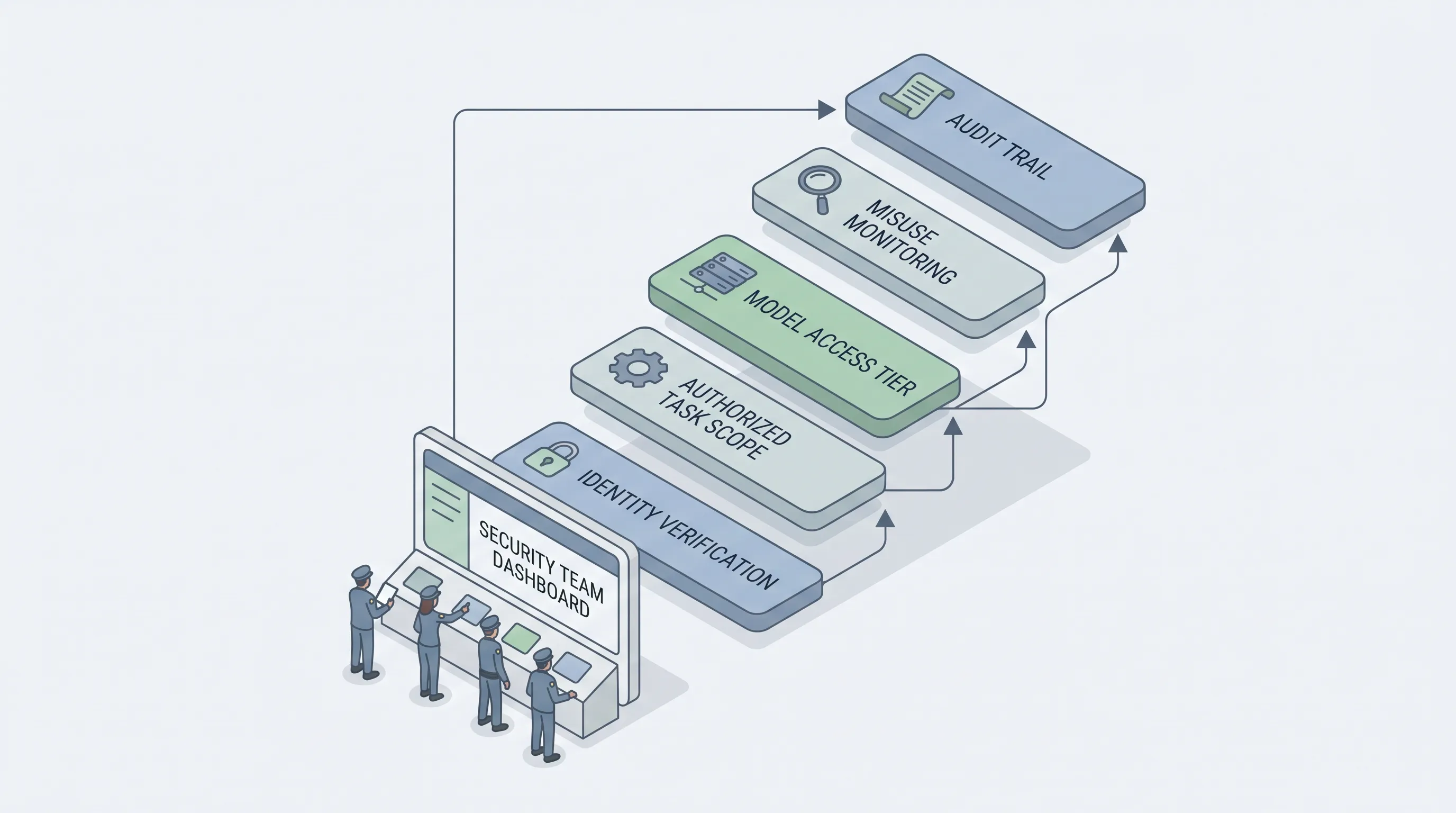
The larger signal is clear: as frontier models become more useful for cybersecurity, access policy becomes part of the product surface. The question is no longer only “can the model do this?” It is also “who is allowed to ask, under what authorization, with what audit trail, and against which systems?”
For security teams, this is the practical takeaway: the next phase of AI-assisted defense will be less about prompt tricks and more about identity, authorization, isolation, monitoring, and accountable workflows.
Source: https://openai.com/index/gpt-5-5-with-trusted-access-for-cyber